Introduction
In today’s healthcare landscape, where cybercriminals increasingly target organizations, the urgency for robust cybersecurity measures is paramount. Endpoint Detection and Response (EDR) stands out as a crucial element in protecting sensitive patient information, providing real-time monitoring and swift responses to potential threats. However, as cyber threats continue to evolve, healthcare IT directors encounter the challenge of effectively implementing and optimizing EDR solutions.
How can these leaders ensure their organizations not only meet regulatory requirements but also remain proactive against malicious actors?
Define EDR and Its Importance in Healthcare Security
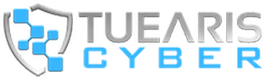
Endpoint Detection and Response (EDR) is a critical cybersecurity technology that continuously monitors endpoint devices for suspicious activities. This capability enables real-time identification, investigation, and response to potential risks. In the healthcare sector, where the protection of sensitive patient information is paramount, EDR protection serves as a primary defense against cyber threats, including ransomware and data breaches. Recent statistics indicate that healthcare organizations have faced a notable rise in cyber incidents, with ransomware attacks affecting 21% of the sector in the past year. This trend highlights the urgent need for robust security measures.
EDR protection not only enhances security but also aids in compliance with regulations such as HIPAA, ensuring that patient information is adequately protected. By consistently monitoring endpoints, EDR can detect unauthorized changes to medical devices, alerting security personnel to potential risks and preventing breaches before they escalate. For example, the PET Imaging Institute has successfully maintained a breach-free status for a decade by utilizing EDR tools in conjunction with expert monitoring, showcasing the effectiveness of this technology in practical applications.
Furthermore, EDR’s advanced analytics capabilities can identify unusual access patterns, which are essential for detecting insider threats and safeguarding patient confidentiality. As medical organizations face increasing regulatory pressures and the need to protect vast amounts of sensitive information, EDR protection emerges as an indispensable resource for IT directors in the sector. It offers both reassurance and a proactive approach to cybersecurity. Tuearis Cyber’s extensive cybersecurity support exemplifies this, as they work closely with medical systems to enhance their security posture and operational control. Their commitment to measurable cybersecurity effectiveness, including reducing false positives and ensuring rapid response times, positions them as a trusted partner in navigating the complexities of cybersecurity within the healthcare domain. As Aviad Hasnis, Chief Technology Officer at Cynet, notes, “EDR solutions can enforce security policies, such as access controls and encryption, to ensure that patient data is protected.
Explore Key EDR Capabilities for Enhanced Threat Detection and Response
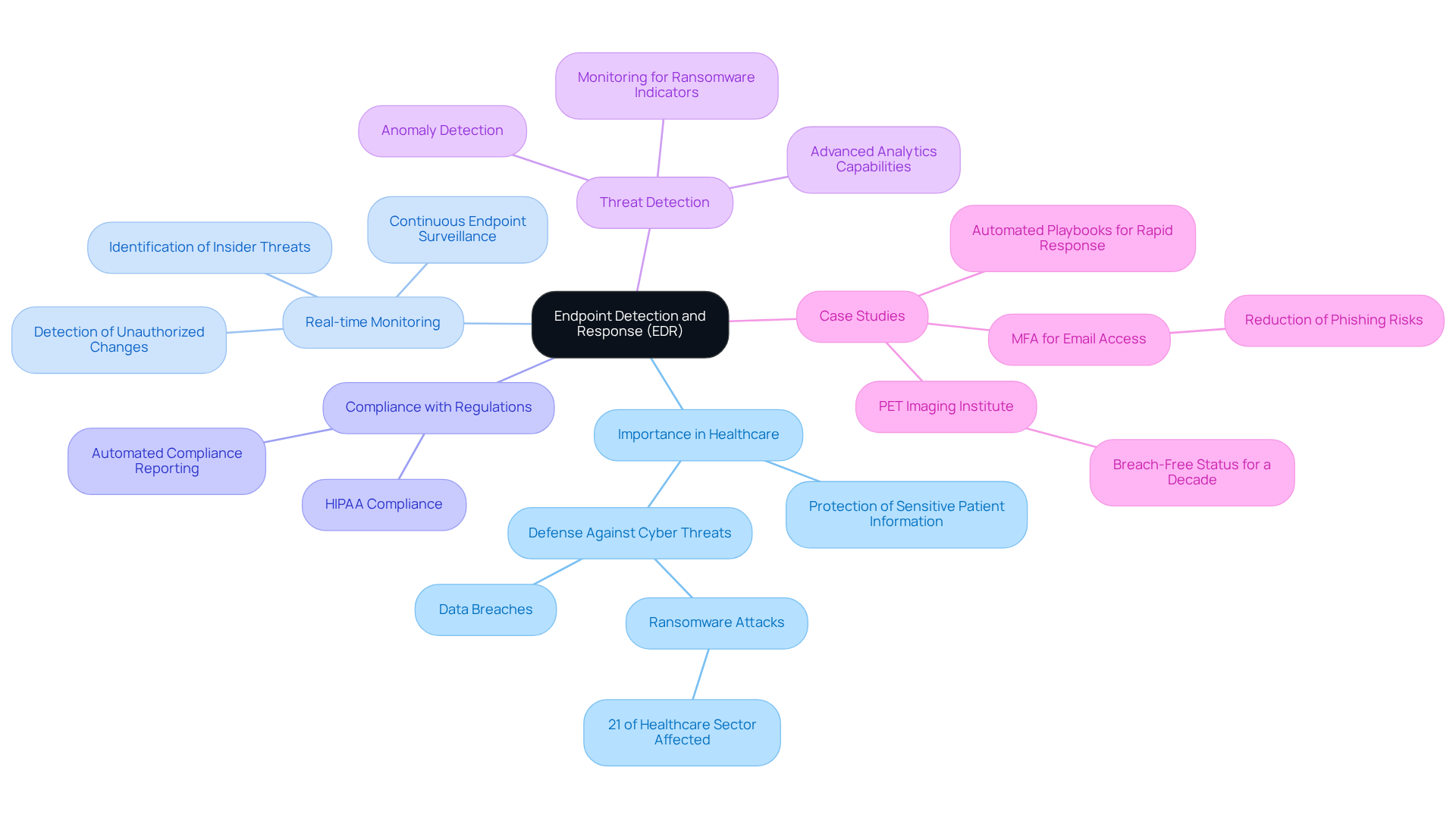
Key capabilities of EDR protection solutions include continuous monitoring, behavioral analysis, and automated response mechanisms, all of which are essential for robust security in the medical field. Continuous monitoring provides real-time visibility into endpoint activities, enabling the swift detection of anomalies that may indicate a security breach. Behavioral analysis employs machine learning to identify unusual patterns that suggest potential threats, thereby enhancing the system’s ability to proactively recognize risks. For instance, an EDR system can automatically isolate a compromised device from the network, effectively preventing the spread of malware and protecting other endpoints.
This proactive approach to EDR protection is particularly crucial, especially as medical institutions have seen a significant rise in cyber risks, with the U.S. medical sector experiencing double the breaches in 2025 compared to the previous year. Furthermore, the integration of automated response features allows for prompt action, ensuring that risks are addressed before they can inflict substantial damage. These advanced capabilities are vital for IT directors in the medical field who are working to fortify their organization’s security framework against evolving cyber threats.
In 2024, organizations utilizing Tuearis Cyber’s XDR solution reported an average reduction in response time of 30%, significantly improving their capacity to effectively mitigate breaches.
Implement EDR Solutions: Strategies for Seamless Integration in Healthcare
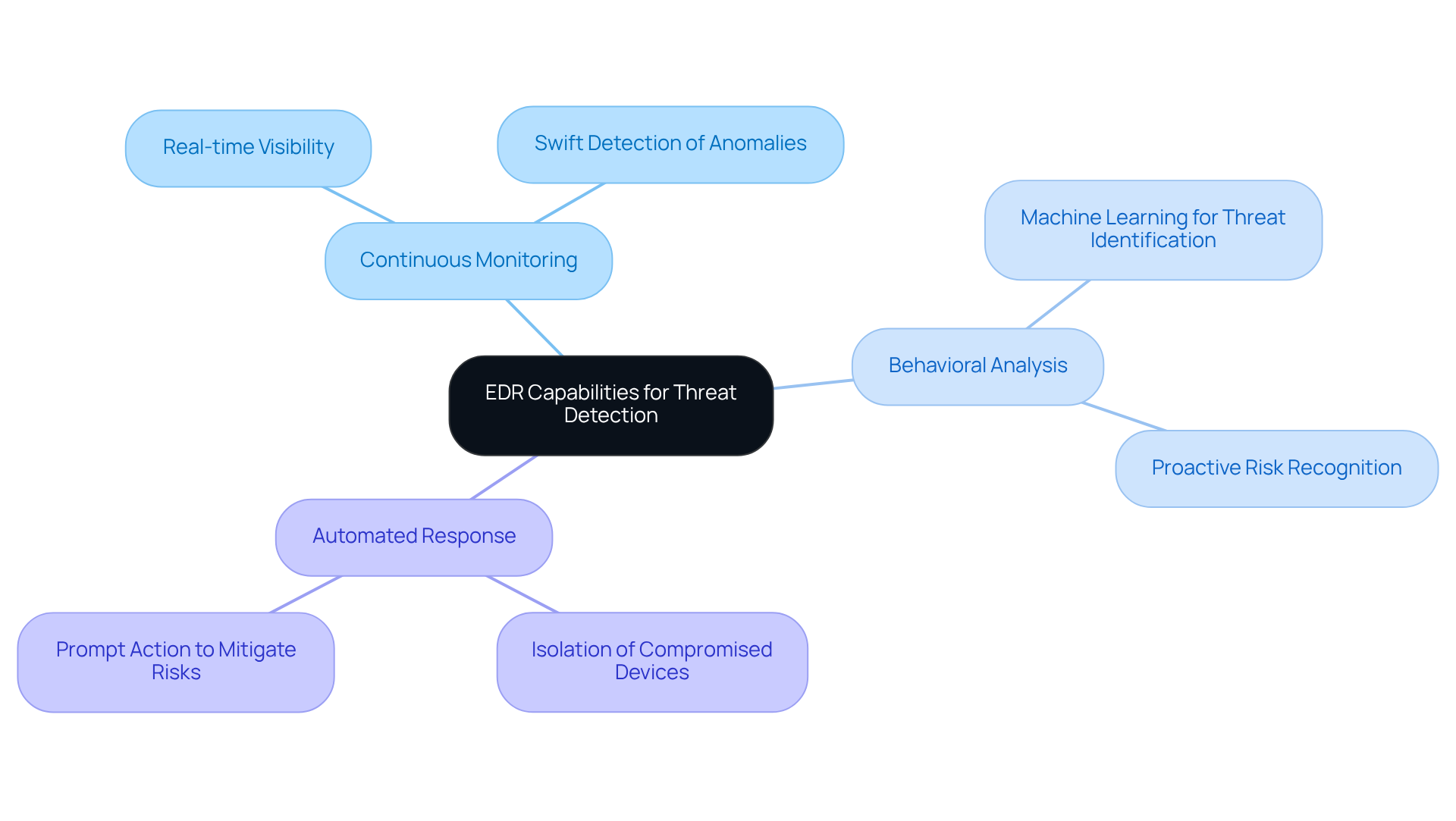
To implement EDR solutions effectively, healthcare IT directors should prioritize several key strategies. First, conducting a thorough assessment of the existing IT infrastructure is essential to identify compatibility with EDR systems. This evaluation must include an analysis of current hardware, software, and network configurations to ensure seamless integration.
Involving stakeholders from various departments – such as clinical staff, compliance officers, and IT personnel – is crucial for aligning the EDR solution with organizational workflows and operational needs. Additionally, training employees on the new system is vital; they must understand how to interpret alerts and respond appropriately to potential risks.
Furthermore, consider a phased implementation approach, starting with critical endpoints before expanding to the entire network. This strategy allows for adjustments based on initial feedback and performance metrics, ensuring a smoother transition and minimizing disruptions to patient care. Regular tuning sessions should be scheduled to review alert patterns and detection effectiveness, thereby enhancing the overall efficacy of the EDR system.
Healthcare entities must remain vigilant against common threats such as ransomware and phishing, which pose serious risks to patient information and compliance with HIPAA regulations. By adopting these best practices and leveraging the rapid incident response capabilities of Tuearis Cyber, medical facilities can maximize the protective capabilities of EDR protection solutions while ensuring adherence to regulatory requirements. For further guidance, refer to our user manuals and FAQs, which provide additional insights into effectively implementing these strategies.
Maintain Continuous Monitoring and Leverage Threat Intelligence for EDR Success
Ongoing observation is crucial for the efficiency of EDR protection solutions, allowing medical institutions to identify risks in real-time and respond swiftly. By integrating intelligence feeds, organizations can significantly enhance their EDR protection capabilities, gaining insights into emerging risks and vulnerabilities specific to the healthcare sector. This proactive approach allows IT directors to adapt their security strategies in response to the evolving risk landscape.
Regular reviews and updates of EDR protection configurations are essential for maintaining effectiveness against new attack vectors. For instance, leveraging attack intelligence can reveal patterns associated with ransomware incidents, empowering organizations to implement preventive strategies before situations escalate. A recent case study illustrates how Tuearis Cyber executed a comprehensive incident response and system recovery within one week following a ransomware attack. They deployed advanced email security measures and initiated a continuous vulnerability management program. This proactive strategy not only facilitated rapid restoration of operations but also thwarted multiple attempted attacks post-recovery, highlighting the tangible benefits of integrating such strategies into cybersecurity frameworks.
Healthcare entities that utilize intelligence on risks have reported a 300% increase in the efficacy of their EDR protection systems, underscoring the critical role of informed decision-making in cybersecurity. Furthermore, organizations that implement role-based access controls (RBAC) alongside threat intelligence have reduced potential losses by an average of $2.4 million, further demonstrating the advantages of incorporating these strategies into their cybersecurity frameworks.
With the Cybersecurity Information Sharing Act of 2015 set to expire in September 2025, the urgency for implementing robust security measures is more critical than ever.

Conclusion
In conclusion, maximizing EDR protection in healthcare is not just a technical necessity; it is a crucial strategy for safeguarding sensitive patient information and ensuring compliance with regulatory standards. By implementing Endpoint Detection and Response (EDR) solutions, healthcare IT directors can create a robust security framework that proactively identifies and mitigates threats, thereby enhancing their organizations’ overall security posture.
Continuous monitoring, behavioral analysis, and automated response mechanisms are essential capabilities of EDR solutions. These features empower healthcare organizations to detect anomalies in real time, respond swiftly to potential breaches, and maintain compliance with regulations such as HIPAA. Additionally, integrating threat intelligence and conducting regular system updates significantly boosts the effectiveness of EDR systems, enabling medical institutions to stay ahead of emerging cyber threats.
Given the escalating cyber risks faced by the healthcare sector, it is imperative for IT directors to adopt these best practices and strategies for seamless EDR integration. Proactive measures not only protect patient data but also foster a culture of security awareness within the organization. By prioritizing EDR protection, healthcare entities can ensure they are well-equipped to navigate the complexities of cybersecurity, ultimately fostering trust and safety in patient care.
Frequently Asked Questions
What is Endpoint Detection and Response (EDR)?
Endpoint Detection and Response (EDR) is a cybersecurity technology that continuously monitors endpoint devices for suspicious activities, allowing for real-time identification, investigation, and response to potential risks.
Why is EDR important in healthcare security?
EDR is crucial in healthcare security as it protects sensitive patient information from cyber threats, such as ransomware and data breaches, which have seen a notable rise in the sector.
What recent trends highlight the need for EDR in healthcare?
Recent statistics indicate that 21% of healthcare organizations faced ransomware attacks in the past year, emphasizing the urgent need for robust security measures like EDR.
How does EDR assist in compliance with regulations?
EDR helps organizations comply with regulations such as HIPAA by ensuring that patient information is adequately protected through continuous monitoring and detection of unauthorized changes.
Can you provide an example of EDR effectiveness in healthcare?
The PET Imaging Institute has maintained a breach-free status for a decade by using EDR tools alongside expert monitoring, demonstrating the practical effectiveness of this technology.
How does EDR help in detecting insider threats?
EDR’s advanced analytics capabilities can identify unusual access patterns, which are essential for detecting insider threats and safeguarding patient confidentiality.
What support does Tuearis Cyber provide regarding EDR?
Tuearis Cyber offers extensive cybersecurity support to medical systems, enhancing their security posture and operational control, while focusing on measurable cybersecurity effectiveness.
What role do EDR solutions play in enforcing security policies?
EDR solutions can enforce security policies, such as access controls and encryption, to ensure that patient data is protected, as noted by Aviad Hasnis, Chief Technology Officer at Cynet.