Introduction
Automated breach and attack simulation (BAS) is becoming an essential strategy within the healthcare sector, where the implications of cybersecurity are particularly significant. Medical institutions are currently confronting a troubling frequency of data breaches, making the adoption of BAS a proactive measure for identifying vulnerabilities and strengthening defenses. As organizations work to implement this technology, they often encounter challenges related to effective deployment and established best practices. Therefore, how can healthcare entities ensure compliance while also bolstering their defenses against the continuously evolving landscape of cyber threats?
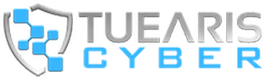
Define Breach and Attack Simulation (BAS)
Automated breach and attack simulation (BAS) represents a proactive cybersecurity strategy that allows organizations to effectively assess their security posture by simulating real-world cyberattacks. By mimicking the tactics, techniques, and procedures (TTPs) used by actual attackers, BAS tools enable entities to identify vulnerabilities and evaluate their defenses against potential breaches.
This approach is particularly crucial in the medical field, where the sensitivity of patient data and the rising incidence of cyber threats present significant risks. In 2023, medical institutions reported an average of 1.99 data breaches involving 500 or more records each day, underscoring the urgent need for robust protective measures. Implementing automated breach and attack simulation allows healthcare institutions to continuously evaluate their protection protocols, ensuring they are prepared to respond effectively to real attacks and mitigate the risk of data breaches.
Tuearis Cyber’s solutions specifically enhance HIPAA compliance and operational safety for multi-site hospital networks, addressing critical gaps in their cybersecurity posture. Additionally, the ‘Protection You Can Measure’ feature, which incorporates Continuous Threat Exposure Management (CTEM), enables organizations to validate which exposures are genuinely exploitable, thereby strengthening their overall security stance.
With measurable effectiveness, Tuearis Cyber minimizes false positives and ensures rapid response times, equipping medical facilities with the necessary tools to bolster their cybersecurity measures through technical safeguards, policy development, and user training.
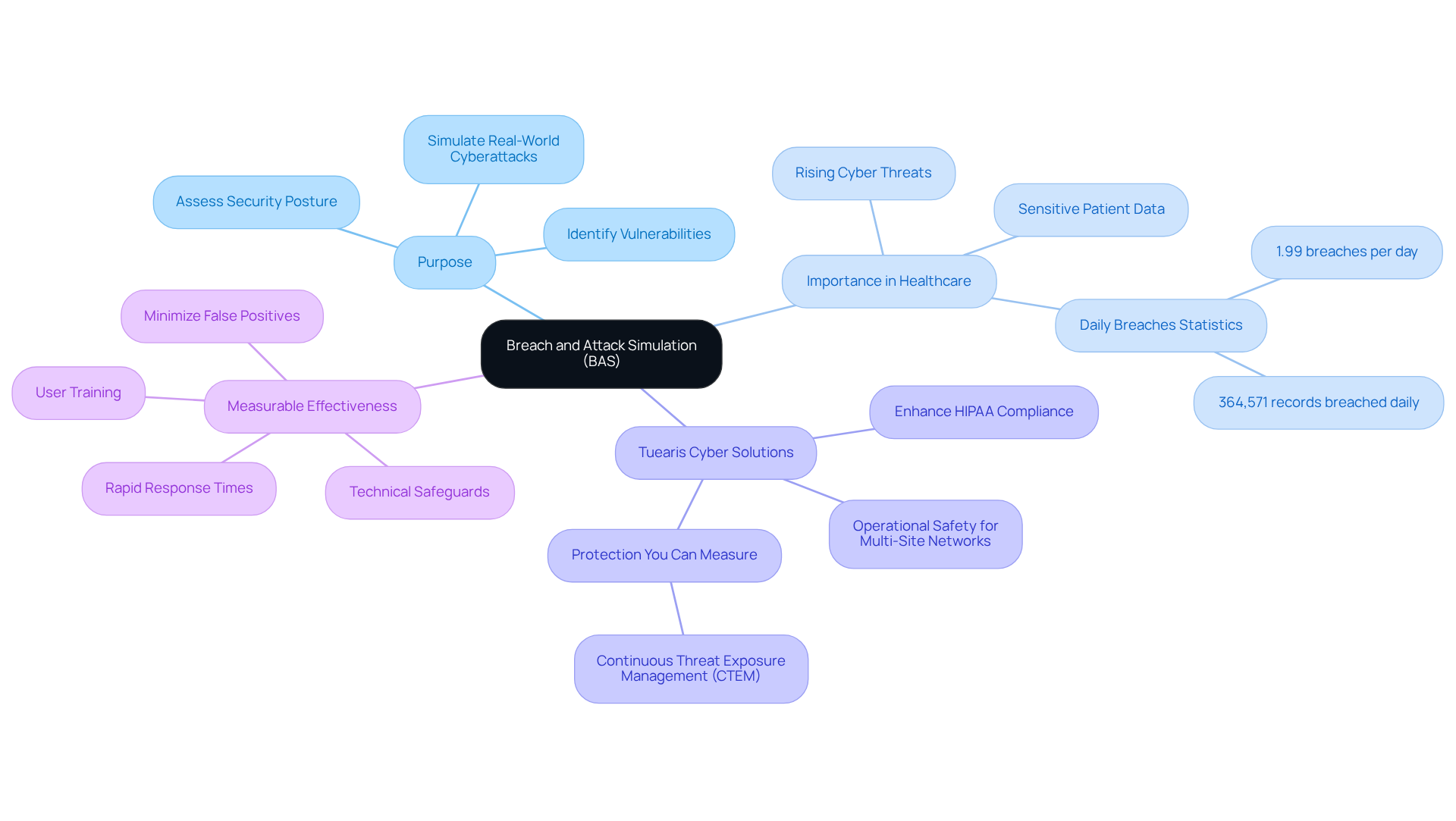
Identify Benefits of BAS for Healthcare Organizations
Implementing Breach and Attack Simulation (BAS) in healthcare organizations offers significant advantages:
-
Enhanced Security Posture: Automated breach and attack simulation proactively identifies vulnerabilities before exploitation occurs, enabling organizations to strengthen their defenses. This continuous validation process, which involves automated breach and attack simulation, ensures that protective measures are effective against real-world threats, thereby significantly reducing the risk of breaches.
-
Regulatory Compliance: With healthcare regulations increasingly demanding robust cybersecurity practices, automated breach and attack simulation assists in compliance by providing documented evidence of ongoing risk evaluations. This is essential for meeting regulatory obligations and demonstrating due diligence in protecting sensitive patient information, which can be achieved through automated breach and attack simulation.
-
Improved Incident Response: By employing automated breach and attack simulation, healthcare organizations can thoroughly assess their incident response capabilities through various simulated attack scenarios. This preparation equips staff to respond swiftly and effectively during actual breaches, leveraging automated breach and attack simulation to minimize potential damage and recovery time.
-
Cost-Effective Protection Testing: Automated breach and attack simulation (BAS) enables continuous vulnerability testing without the extensive resources typically required for manual penetration testing. This efficiency not only conserves time and costs but also delivers ongoing insights into the effectiveness of protective measures through automated breach and attack simulation, allowing for timely adjustments.
-
Stakeholder Confidence: By demonstrating a commitment to cybersecurity through automated breach and attack simulation, organizations can enhance trust among patients, partners, and regulatory bodies. Showcasing a proactive approach to safeguarding sensitive data fosters stronger relationships and confidence in security measures.
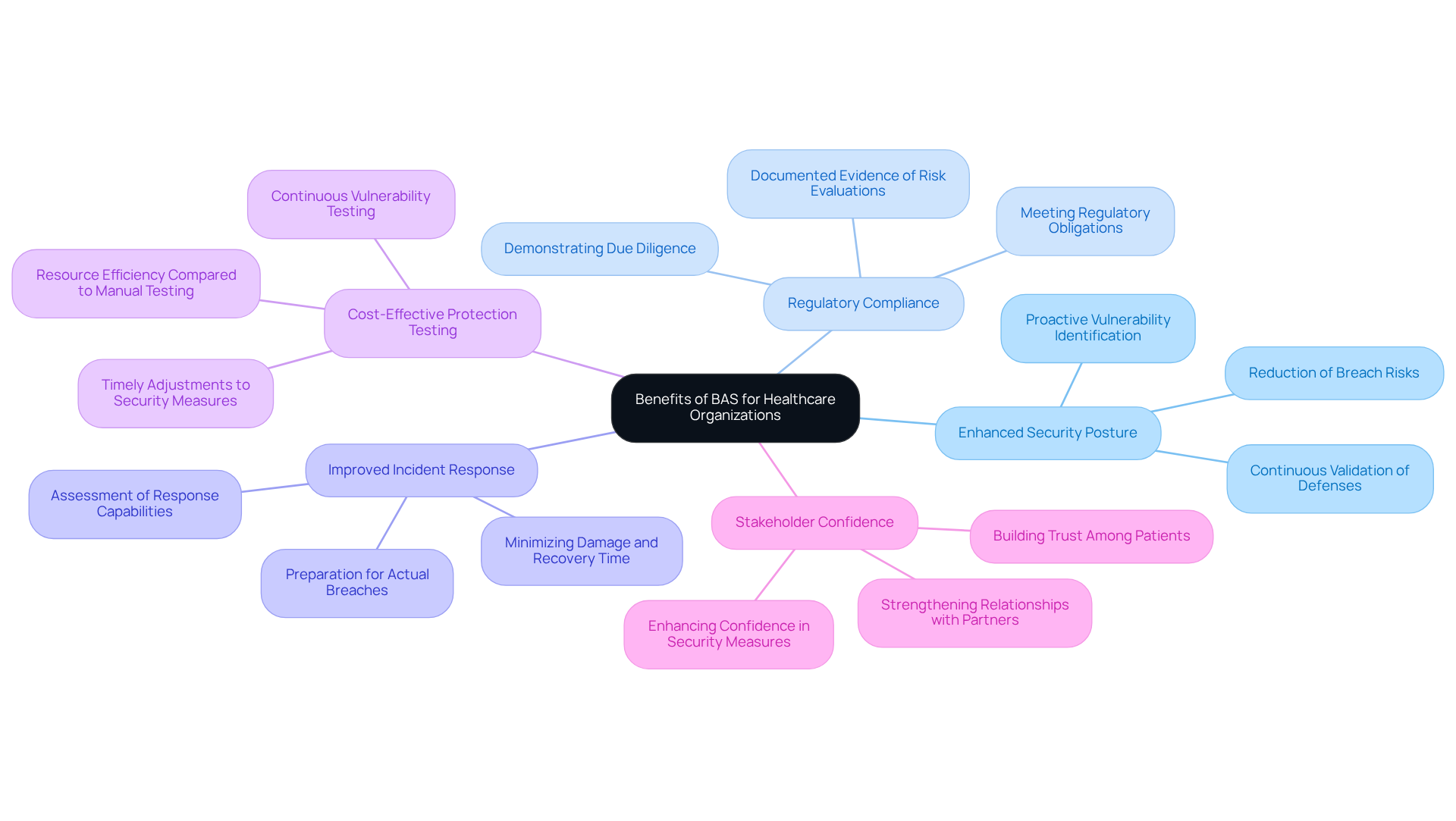
Implement Steps for Effective BAS Deployment
To effectively deploy Breach and Attack Simulation (BAS) in a healthcare organization, follow these steps:
-
Define Objectives: Clearly outline your goals for BAS, such as identifying vulnerabilities, testing incident response capabilities, or ensuring compliance with regulations like HIPAA. Understanding your compliance requirements is crucial for mitigating third-party breaches and strengthening your cybersecurity posture.
-
Select a tool for automated breach and attack simulation that fulfills your entity’s specific needs. Consider factors such as ease of integration, the variety of attack simulations offered, and robust reporting capabilities that align with HIPAA compliance standards.
-
Establish a Baseline: Assess your current security posture to establish a baseline before running simulations. This baseline will act as a reference point to assess enhancements over time and ensure that your entity is ready to handle the intricacies of HIPAA compliance.
-
Schedule Regular Simulations: Implement a routine schedule for running automated breach and attack simulation. Ongoing testing is essential to adjust to the changing threat environment, particularly considering that 92% of medical organizations encountered at least one cyberattack in the past year. Furthermore, with the average expense of a cybersecurity breach in 2024 projected at $4.74 million, regular simulations can assist in reducing potential financial consequences and improving your compliance-driven cybersecurity services.
-
Analyze Results: After each simulation, thoroughly analyze the results to pinpoint weaknesses and areas for improvement. Utilize this data to inform and enhance your overall protection strategy. Keep in mind that 31% of data loss in healthcare organizations is linked to employee carelessness, emphasizing the significance of tackling human elements in your protective measures and strengthening adherence to HIPAA.
-
Engage Stakeholders: Share findings with relevant stakeholders, including IT staff and management, to ensure awareness of vulnerabilities and the proactive steps being taken to address them. Continuous awareness training is crucial to keep staff informed about evolving threats and best practices, especially regarding compliance with HIPAA and other regulations.
-
Iterate and Improve: Use insights gained from simulations to continuously refine your security measures. Automated breach and attack simulation should be regarded as a continuous process instead of a singular occurrence, ensuring that your entity remains resilient against cyber threats and complies with required regulations.
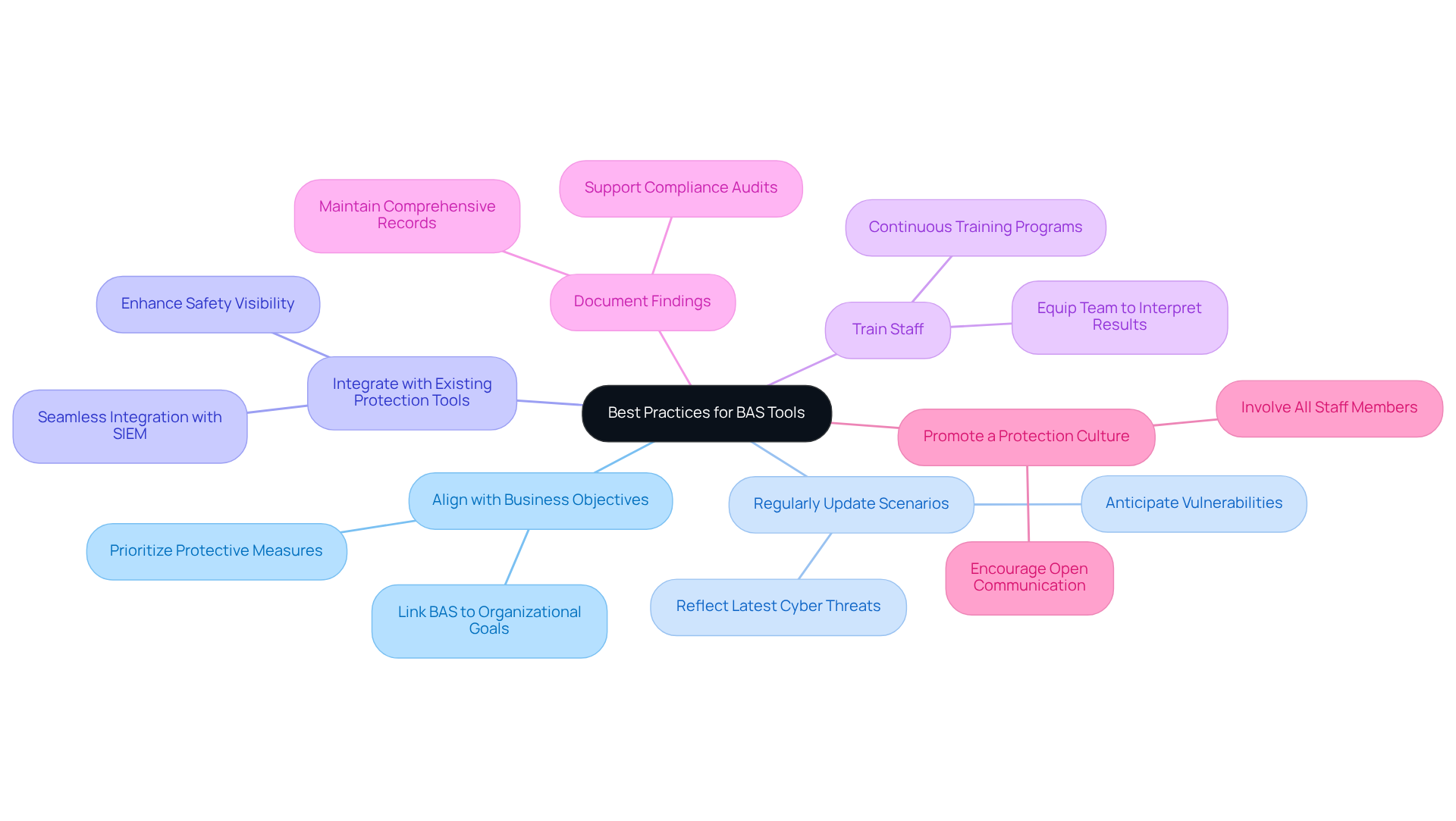
Adopt Best Practices for BAS Tools
To maximize the effectiveness of Breach and Attack Simulation (BAS) tools in healthcare, organizations should adopt the following best practices:
-
Align with Business Objectives: BAS efforts must be directly linked to the overarching goals of the healthcare organization. This alignment prioritizes protective measures that safeguard critical assets, thereby enhancing operational resilience.
-
Regularly Update Scenarios: Given the continuously evolving nature of cyber threats, it is essential to refresh attack scenarios regularly. This practice ensures that the simulations reflect the latest tactics employed by cybercriminals, allowing organizations to anticipate potential vulnerabilities.
-
Integrate with Existing Protection Tools: Seamless integration of BAS tools with current protective infrastructures, such as Security Information and Event Management (SIEM) and Endpoint Detection and Response (EDR) systems, is crucial. This integration enhances overall safety visibility and response capabilities.
-
Train Staff: It is vital to equip the protection team with the knowledge necessary to interpret BAS results effectively and implement required changes. Continuous training ensures a well-prepared team capable of responding swiftly to incidents. Tuearis Cyber emphasizes this training in their comprehensive support services, which have proven to significantly reduce average response times.
-
Document Findings: Maintaining comprehensive records of all simulations, findings, and remediation efforts is invaluable. This documentation supports compliance audits and informs future risk planning, ensuring that lessons learned are applied. In 2024, entities that implemented thorough documentation practices reported a measurable decrease in breach impact.
-
Promote a Protection Culture: Cultivating a culture of protection within the organization involves encouraging open communication about vulnerabilities and protective practices. Involving all staff members enhances overall awareness and promotes shared responsibility for safeguarding patient information. A case study with a regional medical system illustrates how Tuearis Cyber’s method of promoting a protective culture has resulted in improved incident response capabilities.
By adopting these best practices, healthcare organizations can significantly enhance their cybersecurity posture, ensuring that BAS tools not only bolster security measures but also align with the strategic objectives of the organization.
Conclusion
Implementing automated breach and attack simulation (BAS) in healthcare is not just a technical upgrade; it is essential for safeguarding sensitive patient data and enhancing overall cybersecurity. By adopting BAS, healthcare organizations can proactively identify vulnerabilities, ensure compliance with regulations, and improve incident response capabilities. These actions contribute to a more resilient security posture.
The significant benefits of BAS include:
- Enhanced security measures
- Cost-effective protection testing
- Increased stakeholder confidence
These advantages are crucial in a landscape where cyber threats are pervasive, and the consequences of data breaches can be devastating. Furthermore, the step-by-step guide for effective BAS deployment emphasizes the importance of clear objectives, regular simulations, and continuous improvement, ensuring that healthcare entities remain vigilant against evolving cyber threats.
In an environment where the stakes are high, investing in automated breach and attack simulation is a proactive step toward protecting patient information and maintaining trust. Organizations must prioritize BAS as a foundational element of their cybersecurity strategy, fostering a culture of protection that involves all staff members. By doing so, healthcare institutions can not only comply with regulatory demands but also significantly mitigate risks, ultimately leading to safer healthcare environments for all.
Frequently Asked Questions
What is Breach and Attack Simulation (BAS)?
Breach and Attack Simulation (BAS) is an automated cybersecurity strategy that helps organizations assess their security posture by simulating real-world cyberattacks. It mimics the tactics, techniques, and procedures (TTPs) used by actual attackers to identify vulnerabilities and evaluate defenses against potential breaches.
Why is BAS important in the medical field?
BAS is particularly important in the medical field due to the sensitivity of patient data and the increasing incidence of cyber threats. In 2023, medical institutions reported an average of 1.99 data breaches involving 500 or more records each day, highlighting the urgent need for robust protective measures.
How does BAS benefit healthcare institutions?
Implementing BAS allows healthcare institutions to continuously evaluate their protection protocols, ensuring they are prepared to respond effectively to real attacks and mitigate the risk of data breaches.
What specific solutions does Tuearis Cyber offer?
Tuearis Cyber’s solutions enhance HIPAA compliance and operational safety for multi-site hospital networks, addressing critical gaps in their cybersecurity posture.
What is the ‘Protection You Can Measure’ feature?
The ‘Protection You Can Measure’ feature incorporates Continuous Threat Exposure Management (CTEM), enabling organizations to validate which exposures are genuinely exploitable, thus strengthening their overall security stance.
How does Tuearis Cyber improve response times and reduce false positives?
Tuearis Cyber minimizes false positives and ensures rapid response times by providing measurable effectiveness, which equips medical facilities with the necessary tools to enhance their cybersecurity measures through technical safeguards, policy development, and user training.