Introduction
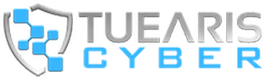
Understanding the complexities of insider threats in healthcare is essential. Internal attacks have surged, with a staggering 83% of medical organizations reporting incidents in 2024. These threats can arise from:
- Malicious actions
- Negligence
- Compromised credentials
They pose significant risks not only to patient data but also to organizational integrity and financial stability.
How can healthcare institutions effectively safeguard against these internal vulnerabilities while navigating the intricate landscape of compliance and patient trust? This article delves into the multifaceted consequences of insider threats and explores proactive strategies that can be implemented to mitigate these risks effectively.
Define Insider Threats and Their Significance
Internal risks within an organization refer to security vulnerabilities that arise from individuals who have authorized access to confidential information and systems. In the medical field, these risks can stem from staff, contractors, or business associates who may inadvertently or deliberately compromise patient information or system reliability. The significance of internal risks in healthcare is profound, introducing unique challenges due to the sensitive nature of health information and stringent regulatory requirements.
For instance, in 2024, medical organizations reported that 83% encountered an internal attack, highlighting the urgency of addressing this issue. Furthermore, the average cost of a healthcare data breach reached $7.42 million, the highest among all sectors, underscoring the financial implications of such risks. Understanding internal risks is crucial for developing effective prevention strategies, ensuring compliance with regulations such as HIPAA, and ultimately safeguarding patient safety.
Case studies, such as the breaches at the Cancer Care Center of North Florida, illustrate the severe consequences of internal threats. Unauthorized access in these instances led to the exposure of sensitive patient health information, including names, addresses, and medical records. By recognizing the various facets of insider threats – malicious, negligent, and compromised – healthcare entities can implement robust security measures and cultivate a culture of cybersecurity awareness to protect patient data effectively.
Additionally, grasping the shared responsibility model in cloud security is vital, as many organizations mistakenly assume that cloud providers manage all security aspects. Tuearis Cyber assists in bridging these gaps by securing what entities possess and ensuring that nothing remains exposed. This collaborative approach enables medical organizations to effectively address these risks.
Identify Types of Insider Threats and Their Motivations
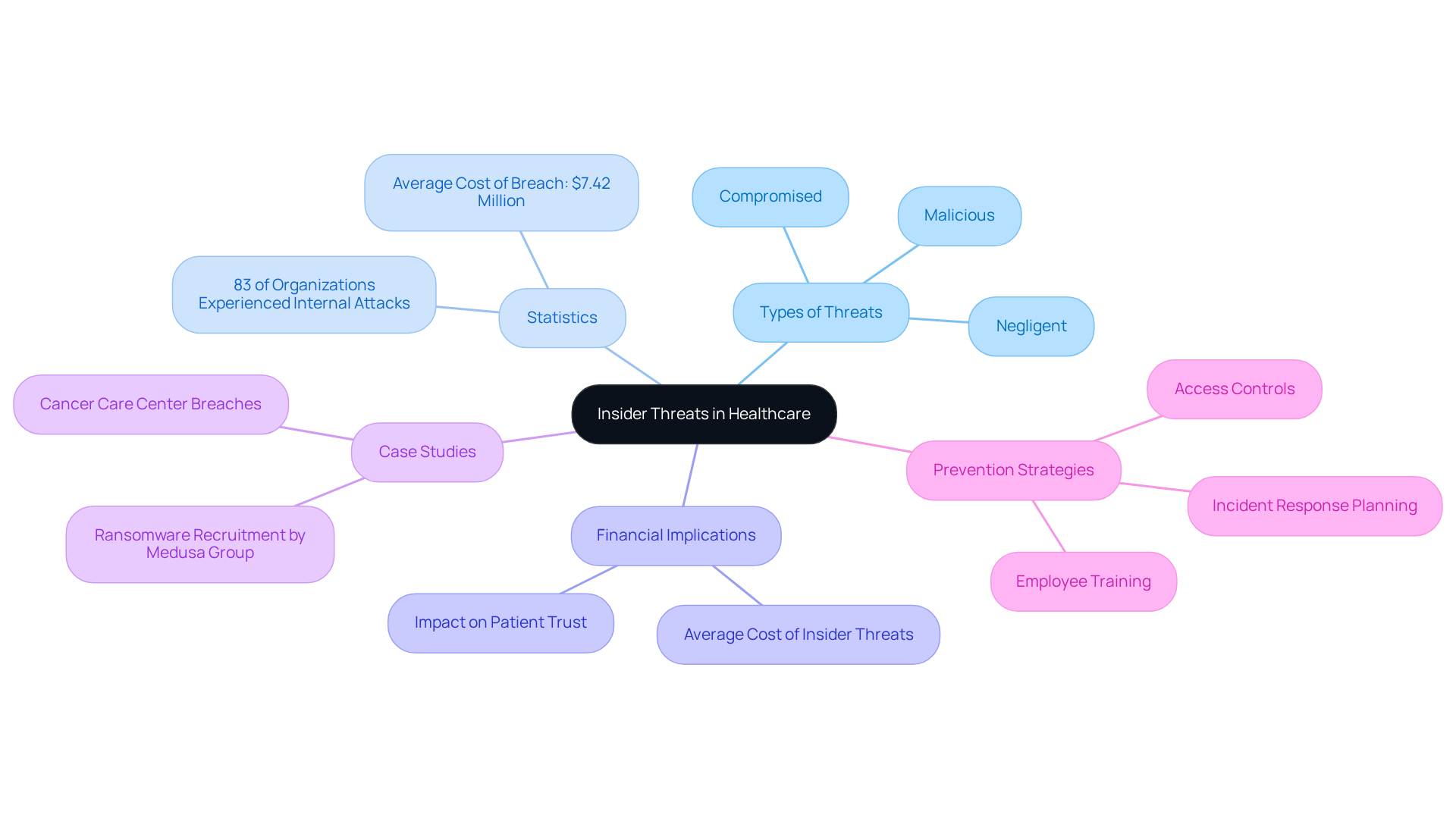
Insider threats in healthcare can be classified into three primary categories, each driven by distinct motivations:
-
Malicious Insiders: These individuals intentionally inflict harm, often motivated by financial gain or personal grievances. For instance, a healthcare employee might steal patient data to sell it on the dark web or to use it for identity theft. The 2024 Verizon Data Breach Investigations Report emphasized that internal risks represented a considerable share of data breaches, with harmful insiders being a primary factor. To combat this, implementing robust technical safeguards, developing comprehensive policies, and conducting recurring audits are essential strategies advocated by entities like Tuearis Cyber.
-
Negligent Insiders: This group comprises employees who inadvertently compromise security through careless actions. Common scenarios include falling victim to phishing scams or mishandling sensitive information, which can lead to unauthorized access or data leaks. A HIMSS survey revealed that nearly 60% of hospital representatives identified emails as the most common cause of data compromise, underscoring the need for robust training programs to mitigate such risks. Moreover, statistics show that 61% of medical data breach risks come from careless employees. By fostering a culture of security awareness and implementing user training, organizations can significantly reduce these risks.
-
Compromised Insiders: These are employees whose credentials have been stolen or misused by external attackers. This situation often arises from sophisticated phishing attacks or malware, which can grant cybercriminals access to sensitive systems. The medical field has observed an increase in such occurrences, with 66% of entities perceiving internal threats as more probable than external assaults. Adopting a Zero Trust approach, as advised by Tuearis Cyber, can assist organizations in better managing these risks by ensuring that access to sensitive information is strictly controlled and monitored.
Understanding the motivations behind these internal threats-ranging from financial incentives to personal grievances-enables healthcare institutions to develop more effective prevention and response strategies. By implementing comprehensive training programs, conducting regular audits, and strengthening cybersecurity controls, organizations can enhance their overall cybersecurity posture.
Examine Consequences of Insider Threats on Organizations
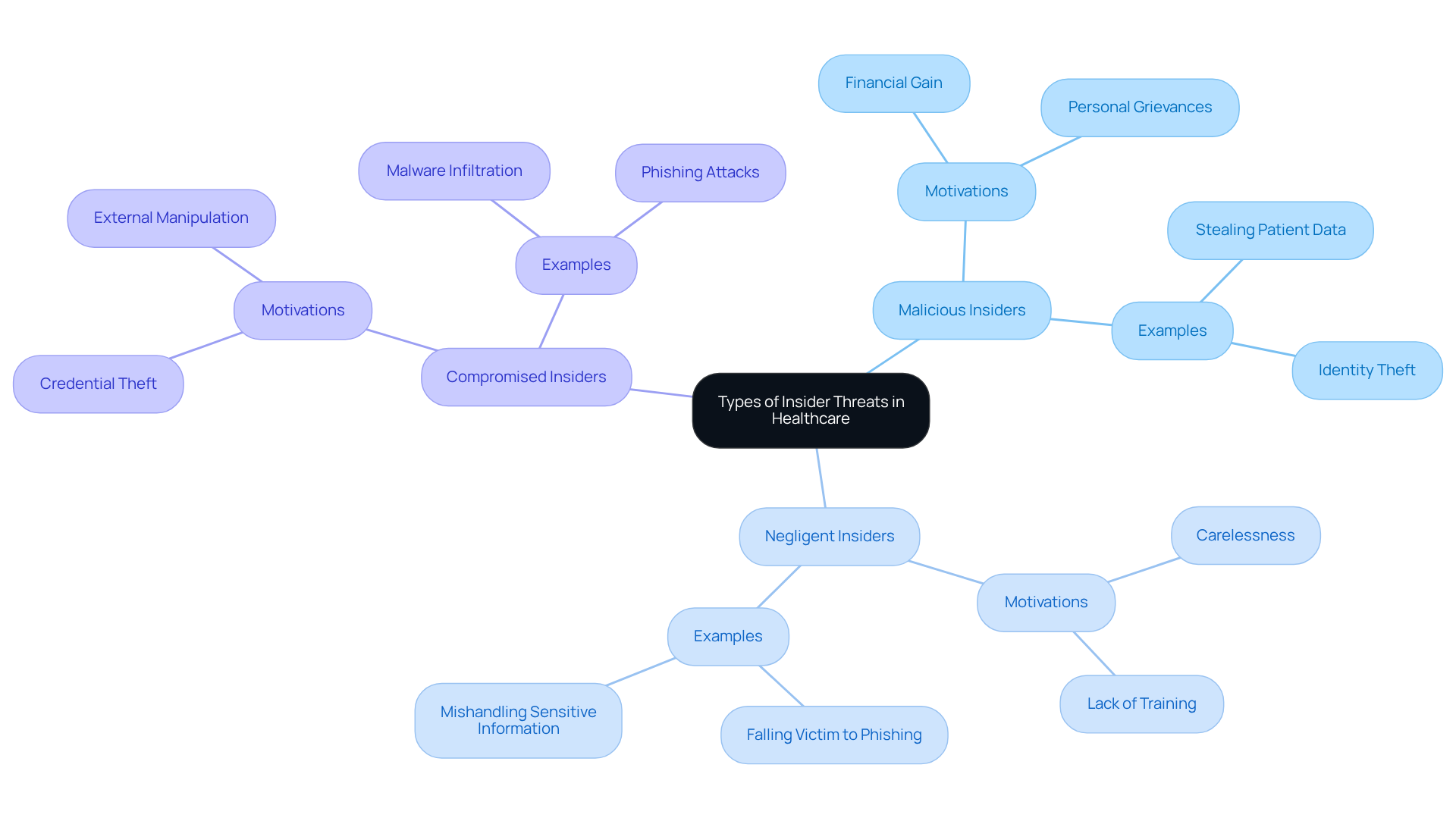
The consequences resulting from an insider threat in healthcare are severe and multifaceted. They include:
-
Data Breaches: Unauthorized access to patient records can lead to identity theft and a significant loss of patient trust. For example, the breach affecting 5.56 million individuals at Yale New Haven Health in March 2025 underscores the critical nature of this issue. Tuearis Cyber’s tailored cybersecurity solutions are specifically designed to address these unique risks, ensuring compliance and protection for sensitive information.
-
Financial Loss: The average expense of a data breach in the medical sector is substantial, often exceeding millions of dollars due to penalties, legal charges, and remediation costs. In 2024, the U.S. Department of Health and Human Services issued $12.84 million in penalties for HIPAA violations, highlighting the financial stakes involved. With Tuearis Cyber’s expertise, organizations can implement proactive strategies to mitigate these financial impacts.
-
Operational Disruption: Insider incidents can disrupt healthcare services, delaying patient care and impacting overall operational efficiency. A ransomware attack on Frederick Health in January 2025 exposed data from 934,000 individuals and caused significant system outages, illustrating how insider threats can lead to critical service interruptions. Tuearis Cyber’s commitment to swift incident response ensures that entities are prepared to manage such disruptions effectively.
-
Reputational Damage: Breaches can tarnish a company’s reputation, resulting in loss of business and diminished patient confidence. The fallout from high-profile breaches, such as the one at Anthem Inc. that affected 78.8 million records, demonstrates how reputational harm can have long-lasting effects on patient relationships and organizational credibility. Testimonials from satisfied clients reinforce Tuearis Cyber’s dedication to security excellence, emphasizing the importance of having a reliable partner in cybersecurity.
Understanding the consequences resulting from an insider threat emphasizes the importance of proactive measures to mitigate internal risks. With Tuearis Cyber’s assistance, medical entities can enhance their security resilience.
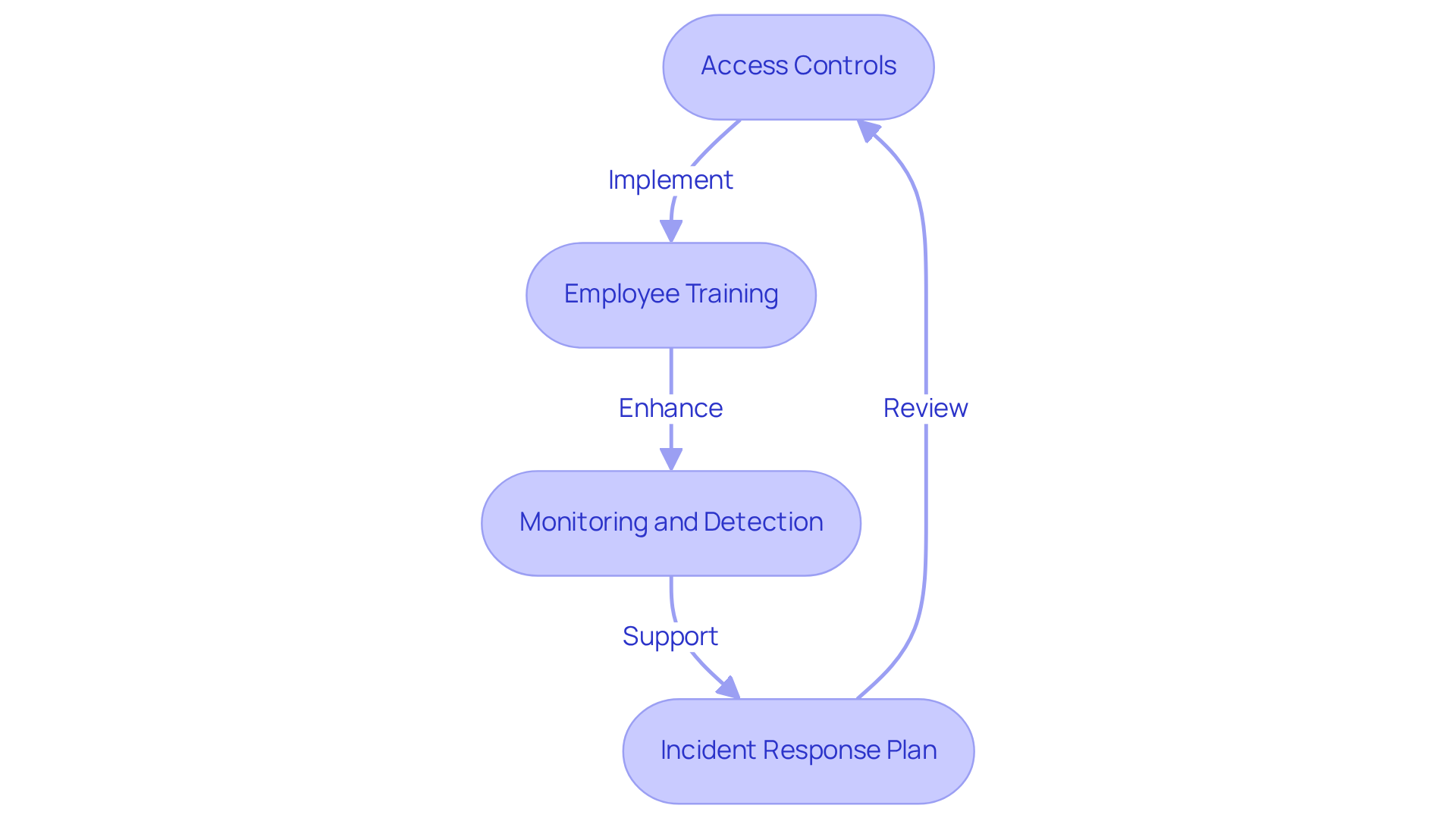
Implement Strategies to Mitigate Insider Threats
To effectively mitigate insider threats, healthcare organizations should adopt several key strategies:
-
Access Controls: Implement stringent access controls and conduct regular reviews of permissions to ensure employees have access only to the information necessary for their roles. This method is essential, as research indicates that excessive access is a frequent cause of insider breaches, with 56% of data breaches in the medical field linked to insider incidents. Tuearis Cyber offers tailored cybersecurity solutions that can help establish these controls effectively.
-
Employee Training: Conduct regular training sessions to educate staff on cybersecurity best practices, including recognizing phishing attempts and understanding the importance of data protection. Ongoing training has demonstrated effectiveness; entities that prioritize security awareness report enhanced compliance with protocols and faster incident reporting. With expert consultation from Tuearis Cyber, organizations can enhance their training programs to address specific vulnerabilities in the healthcare sector.
-
Monitoring and Detection: Employ sophisticated monitoring tools to identify atypical behavior suggestive of internal risks, such as accessing sensitive data outside of regular working hours. Implementing user behavior analytics can significantly enhance the ability to identify potential risks before they escalate. By adopting a Zero Trust approach, as detailed in Tuearis Cyber’s resources, organizations can improve their monitoring capabilities and reduce risks.
-
Incident Response Plan: Create and uphold a robust incident response strategy that outlines procedures for addressing internal risks. This ensures a swift and effective response to any incidents, minimizing potential damage and maintaining compliance with regulations like HIPAA. Tuearis Cyber offers round-the-clock expert incident response services, providing rapid containment, forensics, and recovery assistance to strengthen your organization’s defenses.
By implementing these strategies, healthcare organizations can foster a more secure environment, effectively reducing the risks posed by insider threats and addressing the consequences resulting from an insider threat, while enhancing their overall cybersecurity posture and leveraging the expertise and support of Tuearis Cyber.
Conclusion
Understanding the implications of insider threats in healthcare is crucial for protecting sensitive patient information and ensuring organizational integrity. These internal risks, arising from malicious intent, negligence, or compromised credentials, present significant challenges that can lead to severe consequences for healthcare organizations. Addressing these threats transcends mere compliance; it is a vital aspect of patient safety and trust.
The prevalence of insider threats is alarming, with statistics revealing that a considerable percentage of healthcare organizations have encountered such incidents. The financial impact of these breaches is staggering, with costs soaring into the millions and potential penalties for non-compliance with regulations like HIPAA. Additionally, the operational disruptions and reputational damage that accompany these threats can have enduring effects on patient relationships and organizational credibility.
Proactive measures are essential for mitigating insider threats in the healthcare sector. By implementing stringent access controls, conducting comprehensive employee training, utilizing advanced monitoring technologies, and establishing robust incident response plans, organizations can significantly bolster their cybersecurity posture. The insights provided underscore the necessity of a collaborative approach, leveraging expert resources to strengthen defenses against these internal risks. Taking action now not only safeguards sensitive data but also reinforces the commitment to patient safety and trust within the healthcare system.
Frequently Asked Questions
What are insider threats in an organization?
Insider threats refer to security vulnerabilities that arise from individuals who have authorized access to confidential information and systems, potentially compromising patient information or system reliability.
Why are insider threats significant in the healthcare field?
Insider threats are significant in healthcare due to the sensitive nature of health information and stringent regulatory requirements. They can lead to severe consequences, including data breaches that jeopardize patient safety and incur high financial costs.
What statistics highlight the prevalence of insider threats in healthcare?
In 2024, 83% of medical organizations reported encountering an internal attack, and the average cost of a healthcare data breach reached $7.42 million, the highest among all sectors.
What are the different types of insider threats?
Insider threats can be categorized into three types: malicious, negligent, and compromised individuals who may expose sensitive information.
How can healthcare organizations address insider threats?
Healthcare organizations can address insider threats by implementing robust security measures, cultivating a culture of cybersecurity awareness, and developing effective prevention strategies.
What is the shared responsibility model in cloud security?
The shared responsibility model in cloud security refers to the understanding that while cloud providers offer security measures, organizations must also take responsibility for securing their own data and systems.
How does Tuearis Cyber assist organizations in managing insider threats?
Tuearis Cyber helps organizations by securing their data and ensuring that nothing remains exposed, thereby bridging gaps in security management related to insider threats.